A new malware botnet was discovered targeting Realtek SDK, Huawei routers, and Hadoop YARN servers to recruit devices into DDoS (distributed denial of service) swarm with the potential for massive attacks.
The new botnet was discovered by researchers at Akamai at the start of the year, who caught it on their HTTP and SSH honeypots, seen exploiting old flaws such as CVE-2014-8361 and CVE-2017-17215.
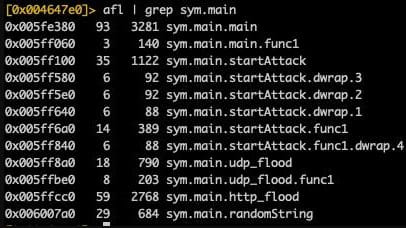
Akamai comments that HinataBot’s operators initially distributed Mirai binaries, while HinataBot first appeared in mid-January 2023. It seems to be based on Mirai and is a Go-based variant of the notorious strain.
After capturing multiple samples from active campaigns as recently as March 2023, Akamai’s researchers deduced that the malware is under active development, featuring functional improvements and anti-analysis additions.
Significant DDoS power
The malware is distributed by brute-forcing SSH endpoints or using infection scripts and RCE payloads for known vulnerabilities.
After infecting devices, the malware will quietly run, waiting for commands to execute from the command and control server.
Akamai’s analysts created a C2 of their own and interacted with simulated infections to stage HinataBot for DDoS attacks to observe the malware in action and infer its attack capabilities.
Older versions of HinataBot supported HTTP, UDP, ICMP, and TCP floods, but the newer variants only feature the first two. However, even with only two attack modes, the botnet can potentially perform very powerful distributed denial of service attacks.
While the HTTP and UDP attack commands differ, they both create a worker pool of 512 workers (processes) that send hardcoded data packets to the targets for a defined duration.
The HTTP packet size ranges between 484 and 589 bytes. The UDP packets generated by HinataBot are particularly large (65,549 bytes) and consist of null bytes capable of overwhelming the target with a large traffic volume.
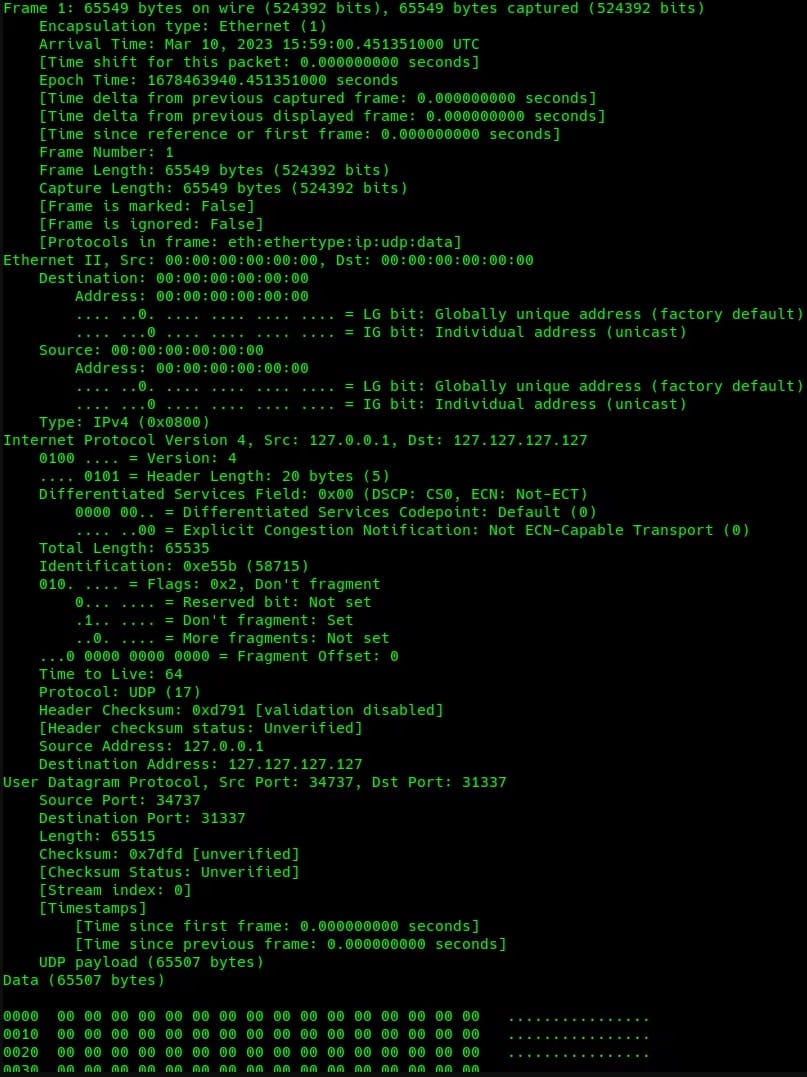
HTTP floods generate large volumes of website requests, while UDP flood sends large volumes of garbage traffic to the target; hence the two methods attempt to achieve an outage using a different approach.
Akamai benchmarked the botnet in 10-second attacks for both HTTP and UDP, and in the HTTP attack, the malware generated 20,430 requests for a total size of 3.4 MB. The UDP flood generated 6,733 packages totaling 421 MB of data.
The researchers estimated that with 1,000…
Click Here to Read the Full Original Article at BleepingComputer…