A malware botnet known as ‘Ebury’ has infected almost 400,000 Linux servers since 2009, with roughly 100,000 still compromised as of late 2023.
ESET researchers have been following the financially motivated malware operation for over a decade now, warning about significant updates in the payload’s capabilities in 2014 and again in 2017.
Below are the Ebury infections logged by ESET since 2009, showing a notable growth in the volume of infections over time.

Source: ESET
In the latest update published today, ESET reports that a recent law enforcement action allowed them to gain insight into the malware operation’s activities over the past fifteen years.
“While 400,000 is a massive number, it’s important to mention that this is the number of compromises over the course of almost 15 years. Not all of those machines were compromised at the same time,” explains ESET.
“There is a constant churn of new servers being compromised while others are being cleaned up or decommissioned. The data at our disposal doesn’t indicate when the attackers lost access to the systems, so it’s difficult to know the size of the botnet at any specific point in time.”
Ebury’s latest tactics
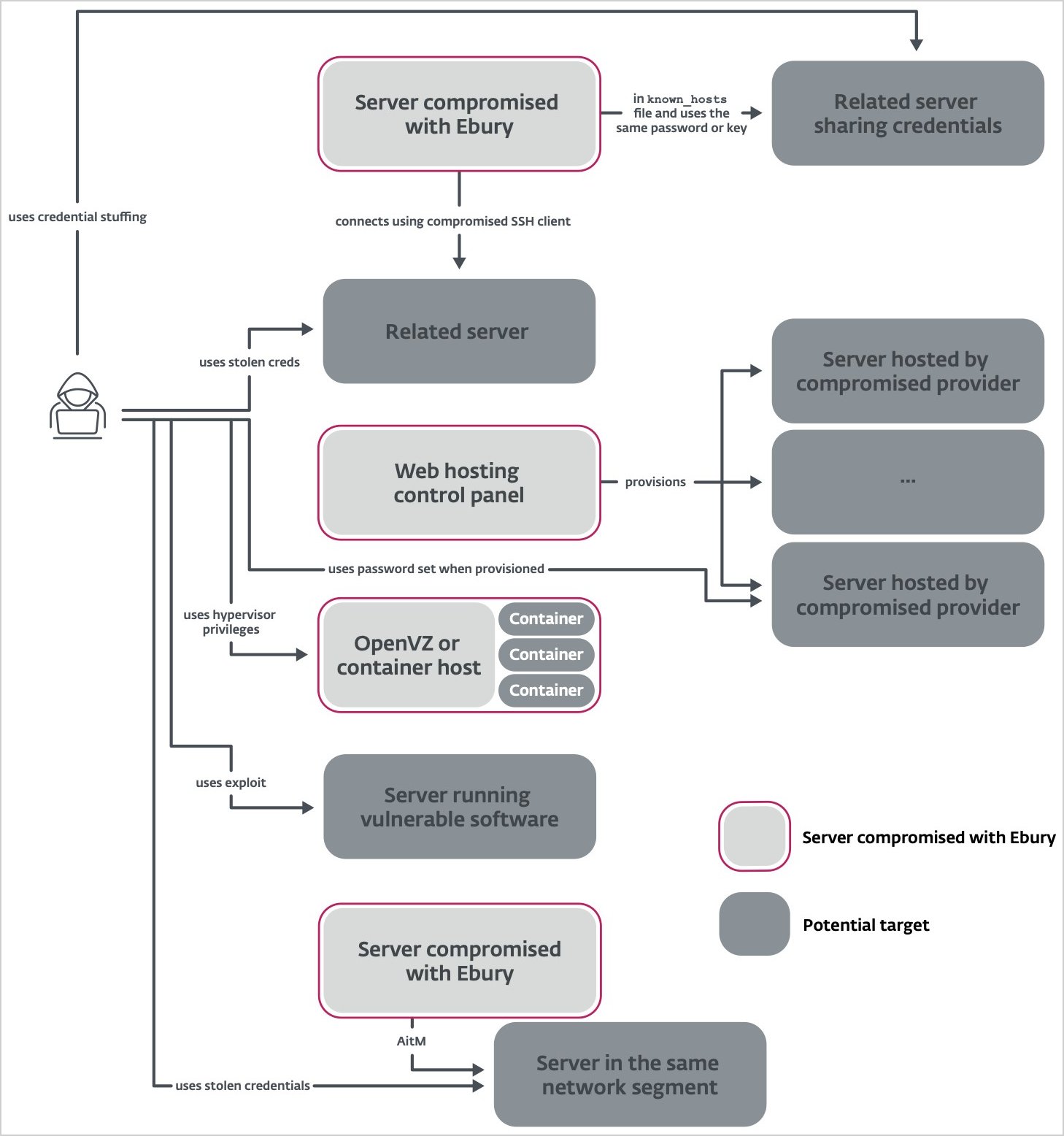
Recent Ebury attacks show a preference by the operators to breach hosting providers and perform supply chain attacks to clients renting virtual servers on the compromised provider.
The initial compromise is performed via credential stuffing attacks, using stolen credentials to log into the servers.
Once a server is compromised, the malware exfiltrates a list of inbound/outband SSH connections from wtmp and the known_hosts file and steals SSH authentication keys, which are then used to try to log into other systems.
“When the known_hosts file contains hashed information, the perpetrators try to brute force its content,” reads ESET’s detailed report.
“Out of 4.8 million known_hosts entries collected by Ebury operators, about two million had their hostname hashed. 40% (about 800,000) of those hashed hostnames were guessed or brute forced.”
Alternatively, and where possible, the attackers may also exploit known vulnerabilities in the software running on the servers to gain further access or elevate their privileges.
Source: ESET
The hosting provider’s infrastructure, including OpenVZ or container hosts, can be leveraged to deploy Ebury across multiple containers or virtual environments.
In the next phase, the malware operators…
Click Here to Read the Full Original Article at BleepingComputer…