Shadow IT – the systems your security team doesn’t know about – is a persistent challenge. Policies may ban them, but unmanaged assets inevitably slip through. And if defenders don’t uncover them first, there’s always a risk attackers will.
With just a few days of effort, Intruder’s security team uncovered multiple real-world examples of Shadow IT exposures: unsecured backups, open Git repositories, unauthenticated admin panels, and more.
Every one of them contained highly sensitive data or credentials, and none required advanced exploitation.
Finding the Targets
One of the most effective ways to uncover Shadow IT is subdomain enumeration. Developers may deploy new systems at will, but to make them accessible they almost always require a subdomain.
We turned to Certificate Transparency (CT) logs, a public ledger of issued TLS certificates. By running wildcard queries and searching for common keywords like “git”, “backup”, or the names of popular software, we quickly uncovered approximately 30 million hosts to work with.
From there, we used a combination of fingerprinting techniques and automated screenshots to determine which hosts were interesting or likely vulnerable. Within days, we had a list of systems exposing critical weaknesses – the kind that attackers routinely exploit at scale.
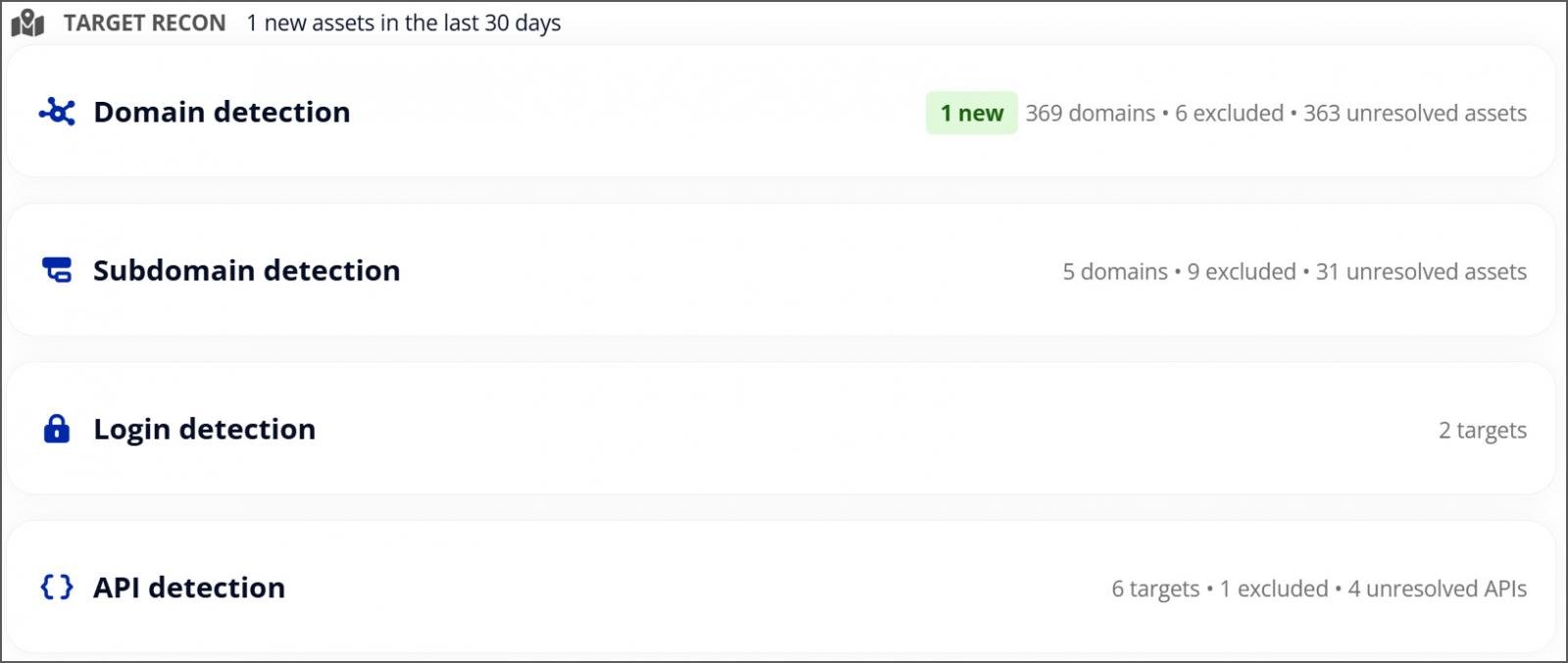
Intruder automatically discovers unknown assets and scans them for exposures before attackers can take advantage – so you can fix real risks fast and stay secure.
Make shadow IT visible. Discover your attack surface with Intruder.
What We Found (In Just a Few Days of Testing)
Vulnerability scanning is ineffective if you don’t know what’s exposed in the first place. Attack surface management solutions like Intruder provide cover on both fronts, helping teams automatically uncover hidden assets and then scanning them for vulnerabilities.
The vulnerabilities that follow are all real exposures on publicly accessible hosts.
Exposed Backups
Backups were among the easiest exposures to uncover. Many backup-related subdomains openly listed directory contents, often with backup archives available for anyone to download.
From just a small sample, we found active credentials and website source code, along with complete database dumps. In one case, the archive even contained hardcoded tokens – including FTP credentials that were still valid at the time of testing.
This kind of exposure is one of the simplest for any…
Click Here to Read the Full Original Article at BleepingComputer…