Three large-scale campaigns targeted Docker Hub users, planting millions of repositories that pushed malware and phishing sites since early 2021.
As JFrog security researchers found, around 20% of the 15 million repositories hosted by Docker Hub contained malicious content, ranging from spam to dangerous malware and phishing sites.
The researchers discovered almost 4.6 million repositories containing no Docker images—which couldn’t be run using a Kubernetes cluster or a Docker engine—and linked approximately 2.81 million to three large malicious campaigns.
Each of these campaigns used different tactics to create and distribute the malicious repositories. The “Downloader” and “eBook Phishing” campaigns created fake repositories in batches, while the “Website SEO” campaign created a few repositories daily and used a single user per repository.
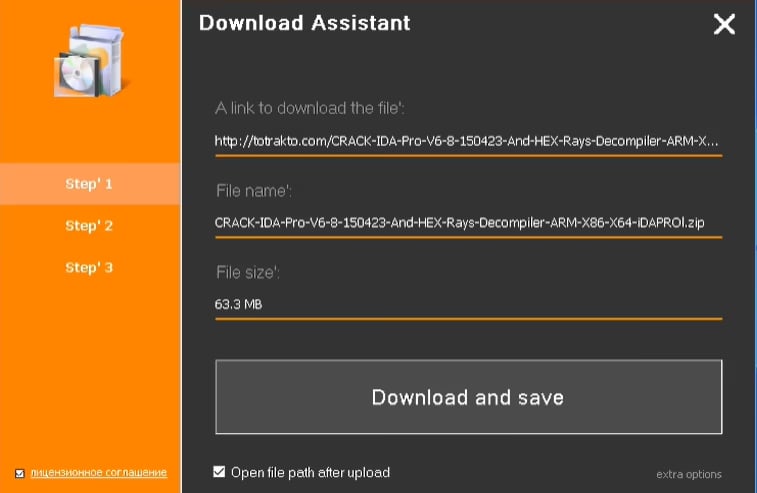
The “Downloader” campaign contained automatically generated texts with SEO text promoting pirated content or cheats for video games and links to the software.
“This campaign operated in two distinct rounds (circa 2021 and 2023), and both rounds used exactly the same malicious payload, a malicious executable that most antivirus engines detect as a generic Trojan,” said JFrog.
When executed, the malware payload it pushed displays an installation dialog that asks the user to download and install the advertised software. However, it will download all the malicious binaries from the offer instead and schedule their persistent execution on the now compromised system.
JFrog suspects that this may be part of a larger malware operation, which could involve adware or monetization schemes that target devices infected after installing third-party software.
The “eBook Phishing” campaign created nearly a million repositories offering free eBook downloads and containing randomly generated descriptions and download URLs. After promising a full free version of an eBook, the website redirects the targets to a phishing landing page asking them to enter their credit card information.
Unlike the previous two campaigns, the “Website SEO” campaign’s aim is unclear. While the content is mostly harmless, all repositories have the same name: “website.”
“It is possible that the campaign was used as some sort of a stress test before enacting the truly malicious campaigns,” said JFrog.
In addition to the large campaigns, smaller repositories with less than 1000 packages were…
Click Here to Read the Full Original Article at BleepingComputer…