North Korean threat actor BlueNoroff has been targeting crypto-related businesses with a new multi-stage malware for macOS systems.
Researchers are calling the campaign Hidden Risk and say that it lures victims with emails that share fake news about the latest activity in the cryptocurrency sector.
The malware deployed in these attacks relies on a novel persistence mechanism on macOS that does not trigger any alerts on the latest versions of the operating system, thus evading detection.
BlueNoroff is known for cryptocurrency thefts and has targeted macOS in the past using a payload malware called ‘ObjCShellz‘ to open remote shells on compromised Macs.
Infection chain
The attacks start with a phishing email containing crypto-related news and subjects, made to appear as if forwarded by a cryptocurrency influencer to add credibility.
The message comes with a link supposedly to read a PDF relating to the piece of information, but points to the “delphidigital[.]org” domain controlled by the attackers.
According to SentinelLabs researchers, the “URL currently serves a benign form of the Bitcoin ETF document with titles that differ over time” but sometimes it serves the first stage of a malicious application bundle that is called ‘Hidden Risk Behind New Surge of Bitcoin Price.app’.
The researchers say that for the Hidden Risk campaign the threat actor used a copy of a genuine academic paper from the University of Texas.
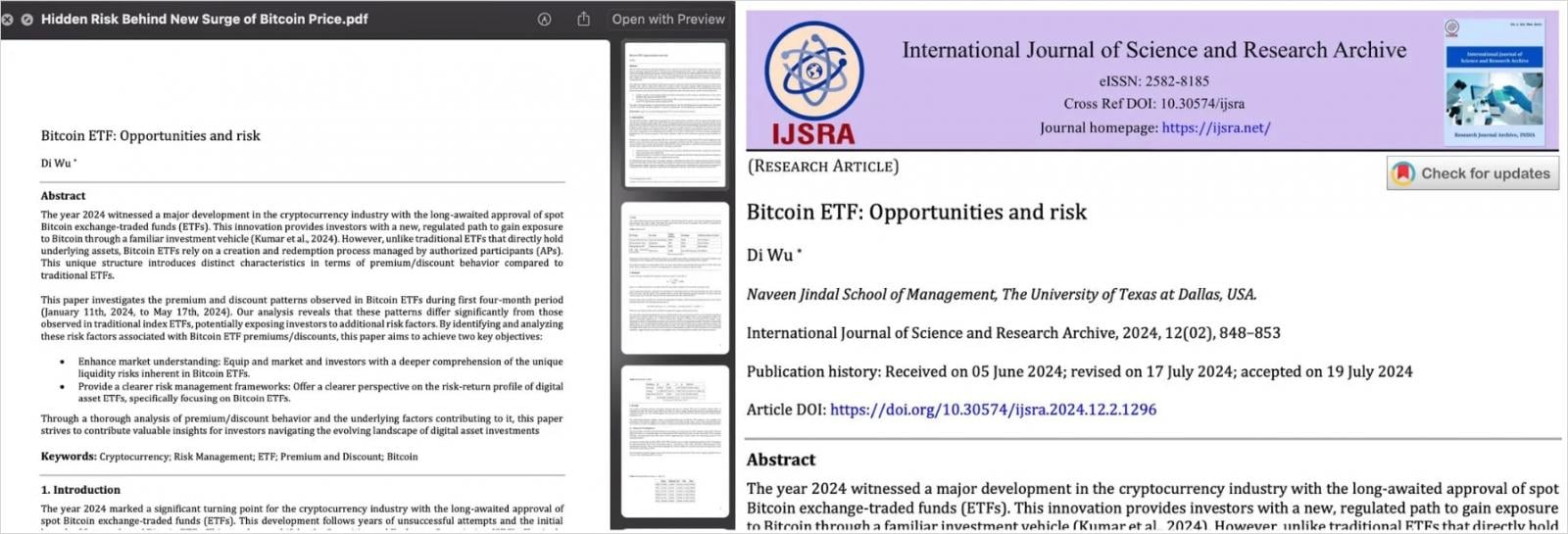
Source: SentinelLabs
The first stage is a dropper app signed and notarized using a valid Apple Developer ID, “Avantis Regtech Private Limited (2S8XHJ7948),” which Apple has now revoked.
When executed, the dropper downloads a decoy PDF from a Google Drive link and opens it in the default PDF viewer to distract the victim. In the background, though, the next stage payload is downloaded from “matuaner[.]com.”
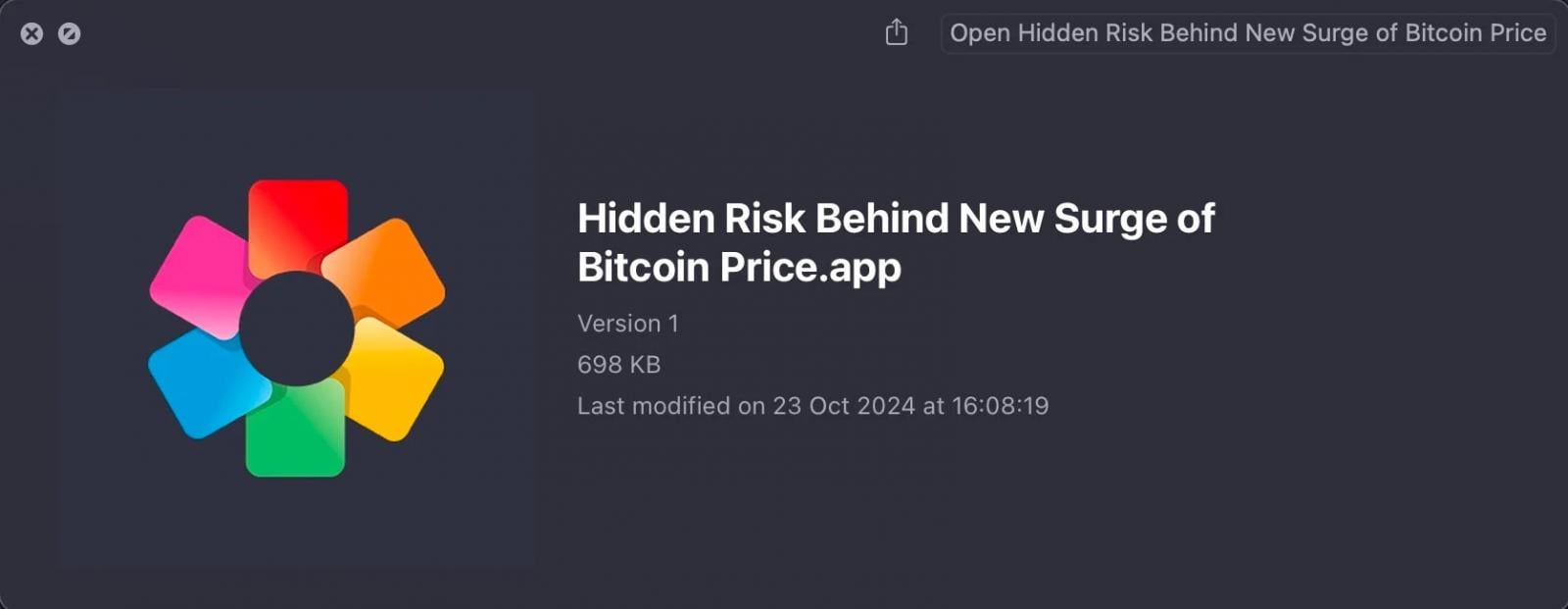
Source: SentinelLabs
Notably, the hackers have manipulated the app’s ‘Info. plist’ file to allow insecure HTTP connections to the attacker-controlled domain, essentially overriding Apple’s App Transport Security policies.
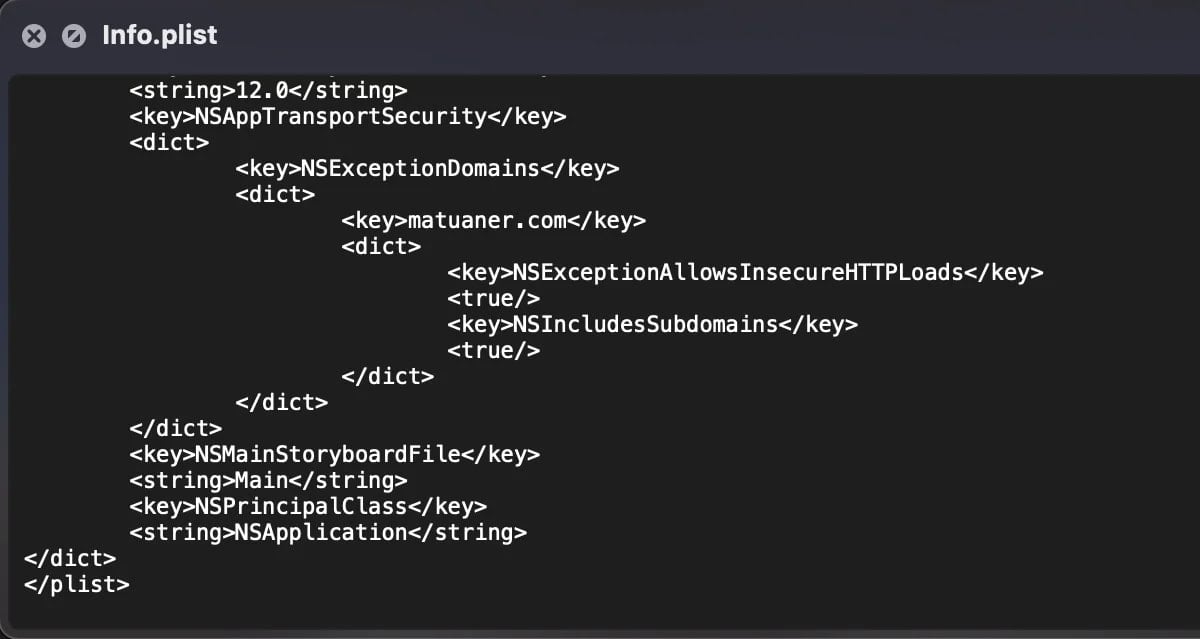
Source: SentinelLabs
Main backdoor and new persistence mechanism
The second-stage payload, called “growth,” is an x86_64 Mach-O binary runs only on Intel and Apple silicon devices that have the Rosetta emulation framework.
It achieves persistence on the system by modifying the “.zshenv” configuration…
Click Here to Read the Full Original Article at BleepingComputer…