Hackers have used new GodLoader malware exploiting the capabilities of the widely used Godot game engine to evade detection and infect over 17,000 systems in just three months.
As Check Point Research found while investigating the attacks, threat actors can use this malware loader to target gamers across all major platforms, including Windows, macOS, Linux, Android, and iOS.
It’s also used to leverage Godot’s flexibility and its GDScript scripting language capabilities to execute arbitrary code and bypass detection systems using the game engine .pck files, which package game assets, to embed harmful scripts.
Once loaded, the maliciously crafted files trigger malicious code on the victims’ devices, enabling attackers to steal credentials or download additional payloads, including the XMRig crypto miner. This miner malware’s configuration was hosted on a private Pastebin file uploaded in May, which was visited 206,913 times throughout the campaign.
“Since at least June 29, 2024, cybercriminals have been taking advantage of Godot Engine to execute crafted GDScript code which triggers malicious commands and delivers malware. This technique has remained undetected by most antivirus tools on VirusTotal, possibly infecting more than 17,000 machines in just a few months,” according to Check Point.
“Godot has a vibrant and growing community of developers who value its open-source nature and powerful capabilities. Over 2,700 developers contributed to the Godot gaming engine,” while “on platforms like Discord, YouTube, and other social media platforms, the Godot engine has around 80,000 followers who stay updated on the latest news.”
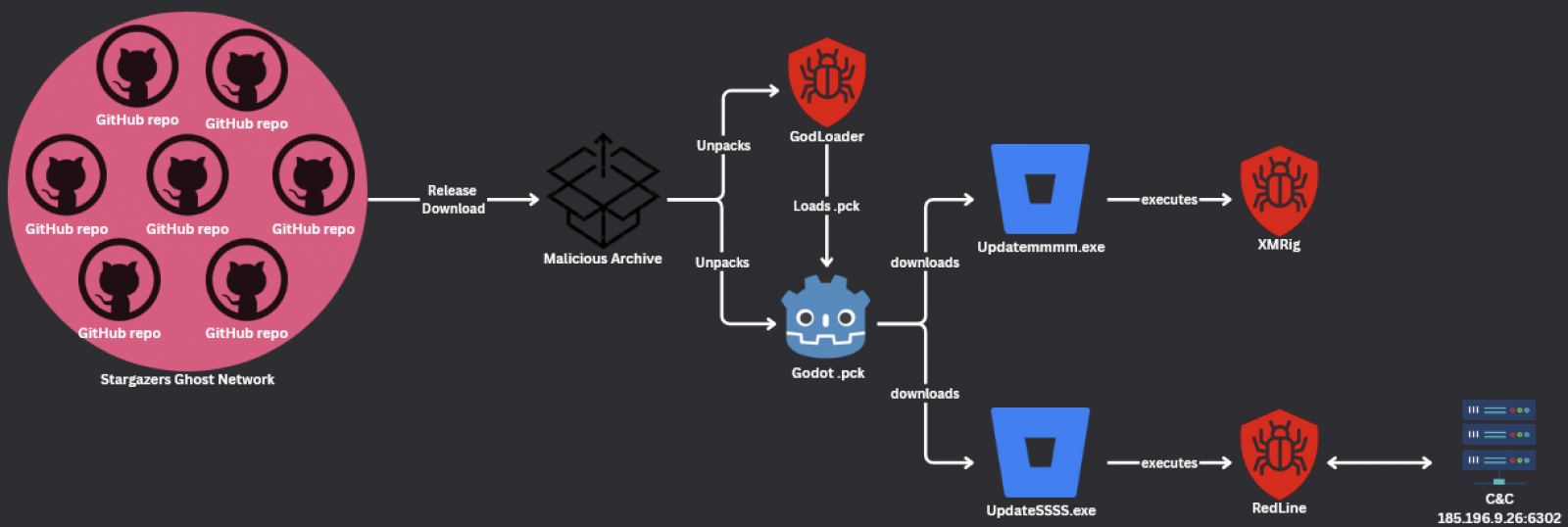
The attackers delivered the GodLoader malware through the Stargazers Ghost Network, a malware Distribution-as-a-Service (DaaS) that masks its activities using seemingly legitimate GitHub repositories.
Between September and October 2024, they used over 200 repositories controlled by over 225 Stargazer Ghost accounts to deploy the malware to targets’ systems, exploiting potential victims’ trust in open-source platforms and seemingly legitimate software repositories.
Throughout the campaign, Check Point detected four separate attack waves against developers and gamers between September 12 and October 3, enticing them to download infected tools and games.
While the security researchers only discovered GodLoader samples targeting Windows systems, they also developed GDScript…
Click Here to Read the Full Original Article at BleepingComputer…